業界知名滲透式測試方法與相關資源

請問業界有沒有比較主流或是知名的滲透式測試方法?
這篇文章主要討論一般業界滲透式測試幾個測試方法
滲透式測試其實並沒有類似ISO的認證機構, 或是 CMMI的模型
來檢視目前測試流程與結果達到什麼等級或是成熟度
因此, 怎樣才是完整的安全測試方法, 或是成熟的安全測試流程就會百家爭鳴
這篇文章的目的主要介紹幾種業界提出的滲透式測試方法論,
讓進行滲透式測試執行時, 可以參考是否有哪些可以學習的地方
- PCI Penetration testing guide
- OWASP testing guide
- Penetration Testing Execution Standard
- Open Source Security Testing Methodology Manual (“OSSTMM”)
- The National Institute of Standards and Technology (“NIST”) Special Publication 800-115
- Penetration Testing Framework
- Mobile Security Testing
- Kali Linux
PCI 滲透式測試方法論
由於PCI機構主要定義 PCI DSS 的電子商務平台認證, 因此這個機構另外建議滲透式測試方法
由PCI 機構的Penetration Test Guidance Special Interest Group共同制訂,
參與的成員包含主要金融機構 Citigroup, American Express, paypal與知名資訊公司IBM, Dell, Cisco, 安全公司paypal等超過100家廠商
https://www.pcisecuritystandards.org/documents/Penetration_Testing_Guidance_March_2015.pdf
PCI建議的測試方法
| 4 Methodology.114.1 Pre-Engagement. 114.1.1 Scoping 11
4.1.2 Documentation . 11 4.1.3 Rules of Engagement. 12 4.1.4 Third-Party-Hosted / Cloud Environments . 12 4.1.5 Success Criteria . 13 4.1.6 Review of Past Threats and Vulnerabilities . 13 4.1.7 Avoid scan interference on security appliances. 14 4.2 Engagement: Penetration Testing 14 4.2.1 Application Layer 15 4.2.2 Network Layer 15 4.2.3 Segmentation . 15 4.2.4 What to do when cardholder data is encountered . 16 4.2.5 Post-Exploitation 16 4.3 Post-Engagement . 16 4.3.1 Remediation Best Practices . 16 4.3.2 Retesting Identified Vulnerabilities. 16 4.3.3 Cleaning up the Environment. 17 |
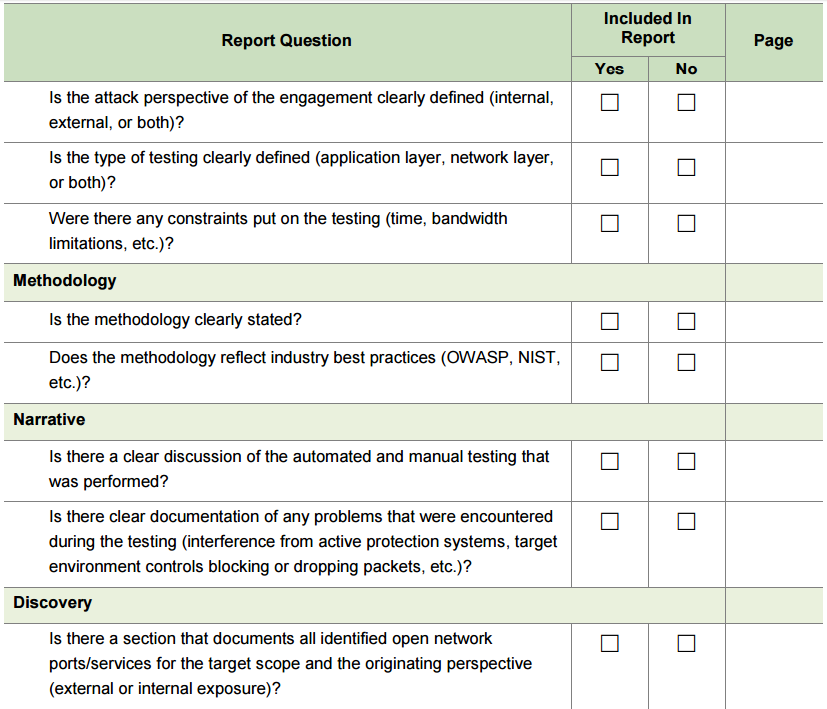
PCI建議的測試報告大綱方法
另外這份文件也建議應該如何提供一個安全測試報告與檢核表
主要大綱包含如下
|
OWASP Testing Guide (筆者推薦)
https://www.owasp.org/index.php/OWASP_Testing_Guide_v4_Table_of_Contents
Penetration Testing Execution Standard (筆者推薦)
http://www.pentest-standard.org/index.php/Main_Page
http://www.pentest-standard.org/index.php/PTES_Technical_Guidelines
- Pre-engagement Interactions
- Intelligence Gathering
- Threat Modeling
- Vulnerability Analysis
- Exploitation
- Post Exploitation
- Reporting
Open Source Security Testing Methodology Manual (“OSSTMM”)
http://www.isecom.org/research/osstmm.html
The National Institute of Standards and Technology (“NIST”) Special Publication 800-115
Penetration Testing Framework
http://www.vulnerabilityassessment.co.uk/Penetration%20Test.html
Mobile Security Testing
http://www.mcafee.com/tw/resources/white-papers/foundstone/wp-pen-testing-android-apps.pdf
https://www.owasp.org/index.php/OWASP_Mobile_Security_Project#tab=Mobile_Security_Testing
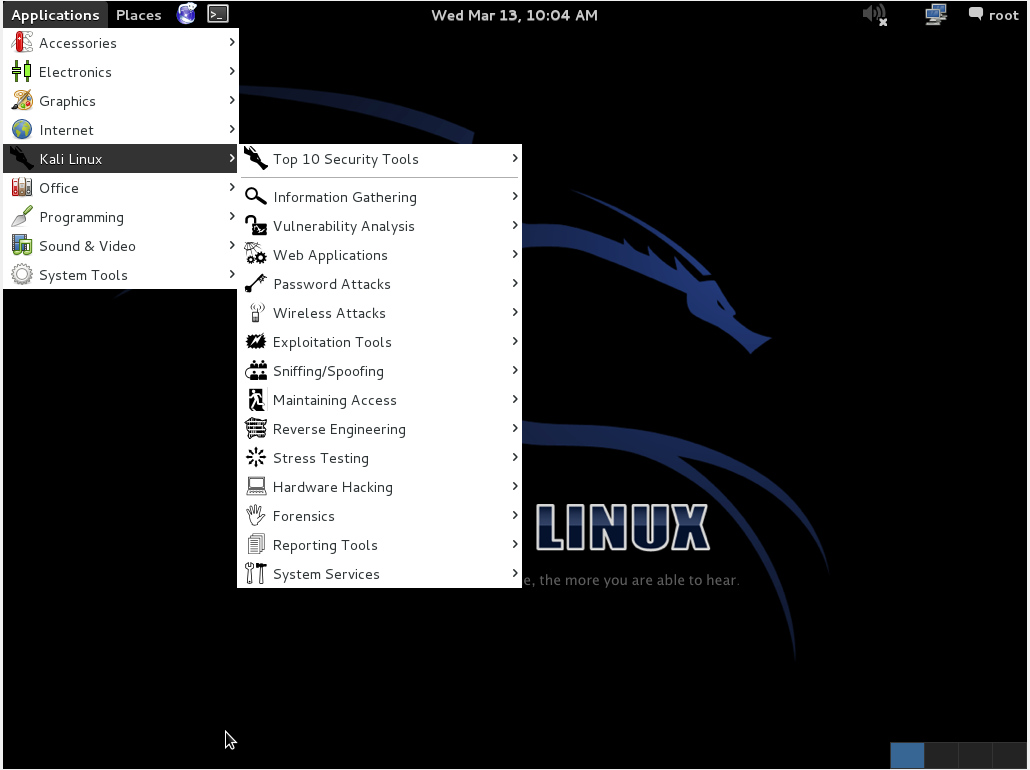
Kali Linux
業界知名的弱點風險參考
National Vulnerability Database (NVD)
Common Vulnerability Scoring System (CVSS)
Common Vulnerabilities and Exposure (CVE)
Common Weakness Enumeration (CWE)
Bugtraq ID (BID)
Open Source Vulnerability Database (OSVDB)